SafeKey was supposed to make checkout safer. Instead, it was making legitimate customers hesitate at the most fragile moment in the journey.

Context
American Express SafeKey was a required authentication step during online checkout. It existed to prevent fraud, but the experience had not kept pace with customer expectations, merchant patterns, or changing regulation.
The redirect into SafeKey often felt abrupt and suspicious. Visual discontinuity, vague messaging, and inconsistent flow logic made people question whether they were still in a legitimate purchase journey.
That made SafeKey more than a security problem. It became a trust problem tied directly to conversion.
Problem
- Customers were abandoning checkout at the redirect to SafeKey.
- The experience looked and sounded disconnected from the merchant flow.
- Users were unsure whether the authentication step was legitimate or phishing.
- Amex and merchants were both losing completed transactions.
- Security requirements could not be relaxed just to improve conversion.
Constraints
- Fraud prevention effectiveness needed to remain intact.
- The redesign had to work across many merchants, devices, and international markets.
- The experience needed to satisfy security and business stakeholders at the same time.
- Any new patterns had to be realistic to implement within existing technical constraints.
Research Findings
The central insight was that users were not rejecting security. They were rejecting ambiguity.
The biggest breakdown happened at the moment of redirect. Once customers lost continuity with the merchant and with American Express, suspicion rose quickly. The old experience made that worse through inconsistent branding, unclear language, and interaction patterns that felt dated and risky.
Research and analysis included:
- Journey mapping from merchant checkout through post-authentication return
- Review of abandonment data and support signals
- Stakeholder interviews across security, business, and engineering
- Competitive analysis of comparable authentication journeys
- Prototype-based user testing with realistic redirect scenarios

Key Decisions
1. Design for reassurance before authentication begins
The experience needed to prepare users for the redirect instead of surprising them with it. Clear pre-authentication messaging and continuity cues reduced the shock of transition.
2. Make legitimacy visible
Brand continuity, recognizable language, and clearer system ownership were treated as functional parts of the flow, not cosmetic cleanup.
3. Reduce cognitive friction in a high-stakes moment
Steps, labels, and interaction states were simplified so users could focus on completing the task rather than deciphering what was happening.
4. Test trust, not just completion
We evaluated not only task success, but also user confidence, hesitation, and perceived legitimacy across redirect scenarios.
System / Workflow / Experience Design
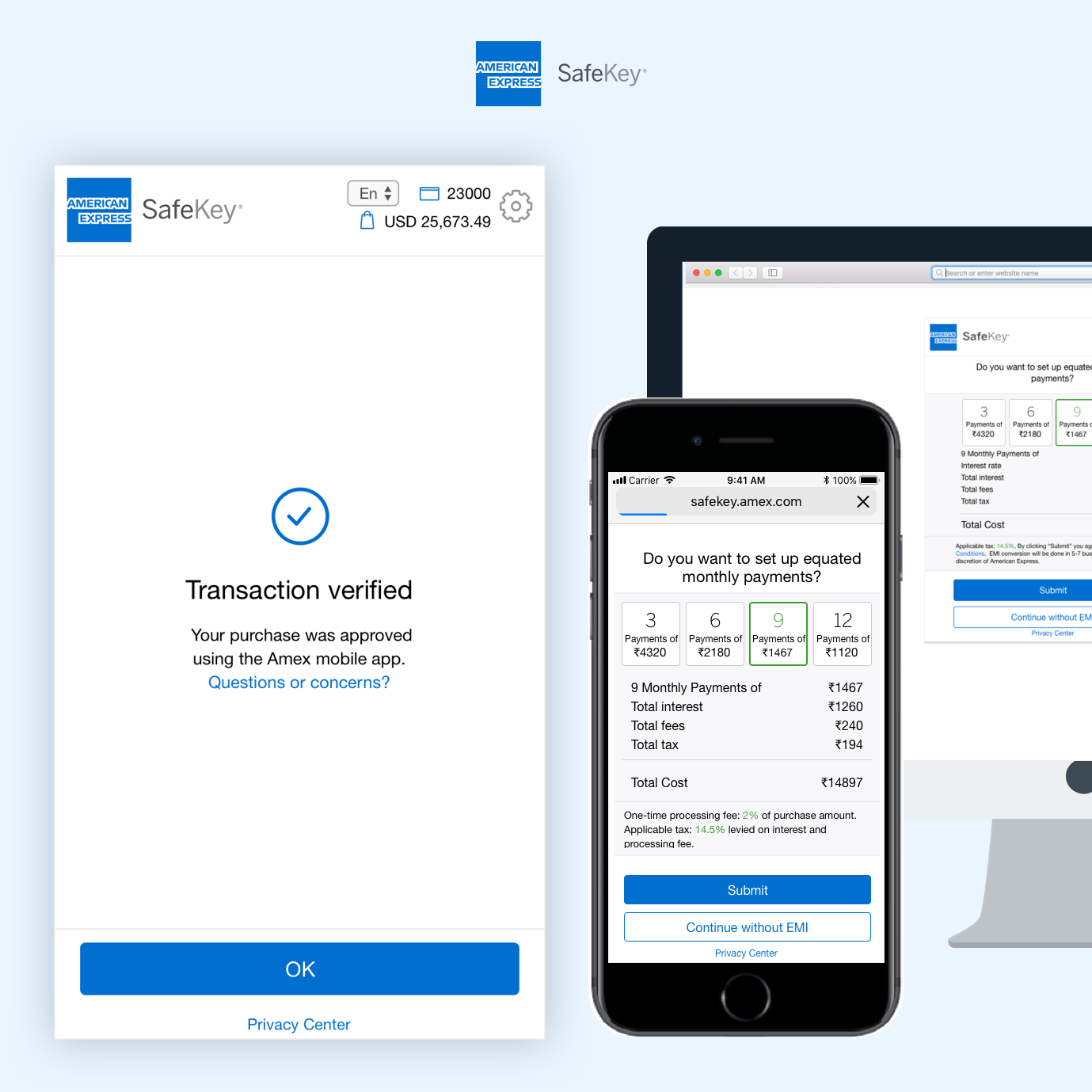
The redesign focused on turning authentication into a coherent extension of checkout rather than an interruption.
Key changes included:
- Pre-authentication messaging to set expectations
- Merchant and Amex continuity cues to reduce perceived risk
- Clearer guidance through the authentication sequence
- Simplified layouts and progress indicators
- Stronger trust signals without undermining security rigor



Validation / Rollout
We built realistic prototypes to simulate redirect-based checkout behavior and used them to test the new journey in conditions close to real purchases.
Validation work included:
- Interactive prototypes for live testing
- Redirect simulations that mirrored real checkout behavior
- Evaluation of confidence, clarity, and task success
- Iteration based on trust breakdowns and hesitation moments
Rollout was phased with technical and organizational alignment:
- Partnered with security and engineering on feasibility and implementation detail
- Created design guidance and specs for scalable rollout
- Launched with lower-risk merchant scenarios first
- Monitored live dashboards and success metrics after release

Outcomes
What I Learned
- Security and UX do not have to compete. The strongest solution improved trust without weakening fraud controls.
- Context changes behavior. When users understand why they are being asked to authenticate, they are far more likely to stay with the flow.
- Trust has to be designed explicitly. Continuity, messaging, and legitimacy cues are core interaction decisions in high-risk moments.
- Realistic testing matters. Redirect-based trust problems do not show up clearly in abstract prototype reviews.